Win 7 Home Security 2011 is a number one threat for computer systems. With this threat ruling a computer system, other infections feel free to destroy and perform a full scope of their malicious activities. That is why it is to be assessed as a superior threat.
Until you get rid of this malware, proper security software will be unable to perform proper system disinfection. However, what good antivirus would do first is the adware detection followed by system adjustment to the state when Win 7 Home Security 2011 removal is possible. Side-effect of such modification may be a temporary disability of some system features, but as soon as the adware is removed they will be restored.
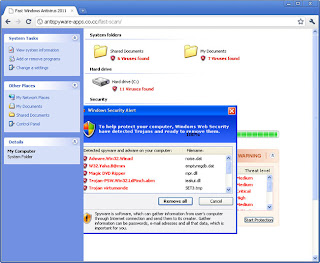
Another aspect related to the adware invasion is its annoying alerting. It keeps users alarmed about numerous virus detections whereas not a single of them has actually been found in the computer memory. The adware does not hesitate to interrupt applications processing current data so that its alerts display often leads to software freezes and current data losses.
Click here to let SpywareDoctor genuine security suite remove Win 7 Home Security 2011.
Malware snapshot:
Win 7 Home Security 2011 remover:
Manual removal instructions:
Delete infected files:
%AllUsersProfile%\t3e0ilfioi3684m2nt3ps2b6lru
%AppData%\Local\.exe
%AppData%\Local\t3e0ilfioi3684m2nt3ps2b6lru
%AppData%\Roaming\Microsoft\Windows\Templates\t3e0ilfioi3684m2nt3ps2b6lru
%Temp%\t3e0ilfioi3684m2nt3ps2b6lru
Delete Win 7 Home Security 2011 registry entries:
HKEY_CURRENT_USER\Software\Classes\.exe "(Default)" = 'exefile'
HKEY_CURRENT_USER\Software\Classes\.exe "Content Type" = 'application/x-msdownload'
HKEY_CURRENT_USER\Software\Classes\.exe\DefaultIcon "(Default)" = '%1' = '"%UserProfile%\Local Settings\Application Data\.exe" /START "%1" %*'
HKEY_CURRENT_USER\Software\Classes\.exe\shell\open\command "IsolatedCommand" = '"%1" %*'
HKEY_CURRENT_USER\Software\Classes\.exe\shell\runas\command "(Default)" = '"%1" %*'
HKEY_CURRENT_USER\Software\Classes\.exe\shell\runas\command "IsolatedCommand" = '"%1" %*'
HKEY_CURRENT_USER\Software\Classes\exefile "(Default)" = 'Application'
HKEY_CURRENT_USER\Software\Classes\exefile "Content Type" = 'application/x-msdownload'
HKEY_CURRENT_USER\Software\Classes\exefile\DefaultIcon "(Default)" = '%1'
HKEY_CURRENT_USER\Software\Classes\exefile\shell\open\command "(Default)" = '"%UserProfile%\Local Settings\Application Data\.exe" /START "%1" %*'
HKEY_CURRENT_USER\Software\Classes\exefile\shell\open\command "IsolatedCommand" = '"%1" %*'
HKEY_CURRENT_USER\Software\Classes\exefile\shell\runas\command "(Default)" = '"%1" %*'
HKEY_CURRENT_USER\Software\Classes\exefile\shell\runas\command "IsolatedCommand" - '"%1" %*'
HKEY_CLASSES_ROOT\.exe\DefaultIcon "(Default)" = '%1'
HKEY_CLASSES_ROOT\.exe\shell\open\command "(Default)" = '"%UserProfile%\Local Settings\Application Data\.exe" /START "%1" %*'
HKEY_CLASSES_ROOT\.exe\shell\open\command "IsolatedCommand" = '"%1" %*'
HKEY_CLASSES_ROOT\.exe\shell\runas\command "(Default)" = '"%1" %*'
HKEY_CLASSES_ROOT\.exe\shell\runas\command "IsolatedCommand" = '"%1" %*'
HKEY_CLASSES_ROOT\exefile "Content Type" = 'application/x-msdownload'
HKEY_CLASSES_ROOT\exefile\shell\open\command "IsolatedCommand" = '"%1" %*'
HKEY_CLASSES_ROOT\exefile\shell\runas\command "IsolatedCommand" = '"%1" %*'
HKEY_CLASSES_ROOT\exefile\shell\open\command "(Default)" = '"%UserProfile%\Local Settings\Application Data\.exe" /START "%1" %*'
HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\FIREFOX.EXE\shell\open\command "(Default)" = '"%UserProfile%\Local Settings\Application Data\.exe" /START "C:\Program Files\Mozilla Firefox\firefox.exe"'
HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\FIREFOX.EXE\shell\safemode\command "(Default)" = '"%UserProfile%\Local Settings\Application Data\.exe" /START "C:\Program Files\Mozilla Firefox\firefox.exe" -safe-mode'
HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\IEXPLORE.EXE\shell\open\command "(Default)" = '"%UserProfile%\Local Settings\Application Data\.exe" /START "C:\Program Files\Internet Explorer\iexplore.exe"'